The Intelligence Platform for Adversarial Risk
Protos AI runs complex, multi-source investigations across the places adversaries operate — the cyber surface, social media, supply chain, and your own workforce — and produces conclusions your team can rely on.
+ Heritage
Founded by operators from the national security community, including Booz Allen Hamilton. Built with a mission-critical customer in 2024., and opened to commercial customers in Q4 2025.
+ Built For
Built for the teams that turn adversarial activity into a conclusion that their organisation can act on.
Hunt threats across your environment, watch for threats targeting your supply chain, and sweep logs when a new advisory drops. Verify remote workers are who they say they are.
Investigate the network behind the case. Enrich alerts and bank statements with counterparty intelligence and cross-domain signals — the investigation layer above your transaction monitoring, not a replacement for it.
Place vendors and counterparties under continuous intelligence, not periodic review. Profile the dependencies behind each vendor, two and three layers deep — the fourth and fifth parties most programmes cannot see.
+ INDUSTRIES WE SERVE
✦ PROBLEM
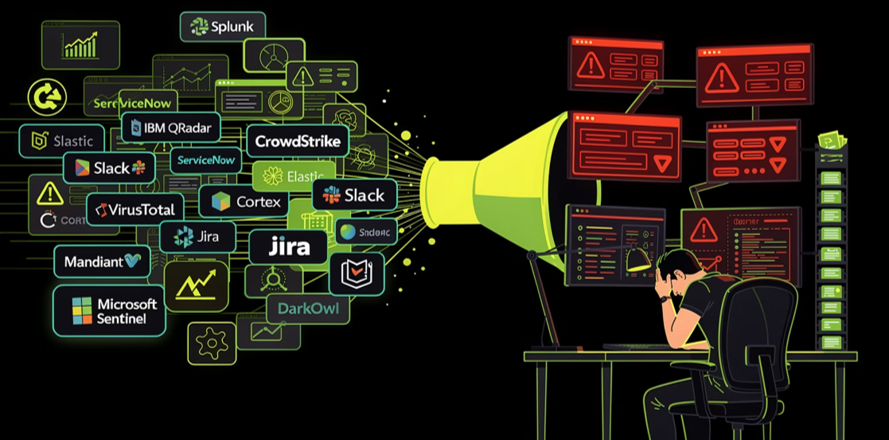
Intelligence teams are losing ground on three fronts: the best people stuck on the wrong work, more data is arriving than any team can process, and adversaries now moving at machine speed.
Senior investigators spend their day on triage, enrichment, and report formatting — work tools or juniors should handle. The judgement you hired them for gets the leftover hours.
27% of organisations now report breaches tied to skill gaps (SANS 2026).
Feeds, alerts, advisories and text documents pile up faster everyday. Working out what any of it means for your environment still depends on a senior investigator at the keyboard.
Vulnerabilities are weaponised in hours. Fraud typologies spread across institutions in days. A compromised supplier can sit undetected for months. The investigation that follows still takes a senior investigator — and time you don't have.
+ SOLUTION
Protos AI does the analytical work between the data and the decision — the work the existing stack leaves to the senior analyst.
AI agents investigate across every adversarial context that touches the enterprise — cyber, social media, supply chain, your own workforce — and across every evidence format the work requires. Structured and unstructured. PDFs, screenshots, emails, logs, transactions, social media signals.
Every investigation produces a conclusion: the actor, the infrastructure, the affected assets, the next step. With the evidence attached. The tradecraft compounds in the platform — not in the analyst who is about to leave.
Not enriched indicators. Not a response playbook. A conclusion your team can rely on.

+ where this is going
Most agentic AI tools will be commoditised. What makes Protos AI still matter in years to come is what we're building towards. We call this - 3C Framework - Compounding, Cross-domain, and Collective Intelligence - and it is how we think about building a platform that earns its position as the category matures.
Every investigation informs the next. Agents build a persistent record of your environment, your adversaries, and your prior work, so the thousandth case is shaped by all the ones before it. Tradecraft no longer leaves the organisation when an analyst does.
Specialist agents work across cyber, financial crime, and supply chain, and connect activity that no single-domain tool can see alone. A phishing email, a fraudulent transaction, and a compromised vendor are often the same adversary. The connection is what matters.
When one customer's agents identify a new adversary pattern, every customer benefits — privately and with consent. In development; we are selecting the initial cohort now.

Five years ago, a platform like this would have required a research lab and millions of users doing intel work. Agentic AI is what makes it possible today. Not the destination — the workforce that gets us there.
+ USE CASES
+ USE CASES
Our AI agent serves as a junior cyber threat intelligence analyst — delivering across core CTI use cases, autonomously and at scale.
Autonomously enrich indicators, map MITRE ATT&CK techniques, and analyze supporting infrastructure — eliminating manual lookups.
Continuously monitor vendors for active targeting. Protect vendors without in-house CTI capabilities.
Identify CVEs from threat advisories and map to impacted assets. Automate regulatory advisory responses.
Analyze logs for IOCs from newly published threat reports. Parse raw logs, flag malicious behavior against known threats.
Identify linkages between disparate malware or phishing incidents. Deep link analysis uncovering hidden cross-campaign connections.
Correlate logs across tools to build a clear end-to-end attacker activity timeline — no manual console switching.
+ USE CASES
Our AI agent serves as a junior investigation analyst — delivering use cases across cyber insurance, financial crime, trade compliance and risk intelligence.
CYBER INSURANCE
Cross-validate proposal forms, underwriting guidelines and attack surface scans for better risk decisions.
CYBER INSURANCE
Scan your insurance portfolio to detect exposure to a new vulnerability. What took days, now takes minutes.
FINANCIAL CRIME
Reduce false positives by prioritising alerts based on behavioural risk, materiality, and context.
FINANCIAL CRIME
Identify emerging fraud patterns and control gaps by analysing confirmed fraud cases and transaction behaviour.
TRADE COMPLIANCE
Improve sanctions decisions by contextualising counterparties, transactions, and jurisdictions against true compliance risk.
COMPLIANCE
Accelerate onboarding by synthesising vendor data, intelligence and risk signals into clear, defensible assessments.
The capabilities below were first built for mission critical operational environments. They are now available to commercial enterprises that need the same.
Use Cases
Agents take raw indicators — IPs, hashes, domains — and return what each one is, who uses it, and what it does in practice. Related infrastructure, the threat actors behind it, and the ATT&CK techniques in play all surface in one pass. What used to require six tabs now lands in one view.
Autonomously enrich indicators, map MITRE ATT&CK techniques, and build actor-linked correlation graphs — without manual pivoting.
Threat Intel
Reported emails return with attribution, infrastructure, the employees targeted, and a containment recommendation. The analyst reviews and decides; they are not starting from scratch.
Continuously monitor vendors for active targeting, exposure events, and threat actor mentions across OSINT, dark web, and breach feeds.
Threat Intel
A threat advisory arrives. Protos AI extracts the indicators and techniques, maps them to your environment, and sets out what to hunt, patch, or block. The advisory becomes a plan, not another document to read.
Identify CVEs from threat advisories and map to impacted assets in your environment, with EPSS-driven prioritisation.
Vulnerability Management
When a vulnerability is disclosed overnight, Protos AI searches months of your logs for exploitation indicators and maps the disclosure to your exposed assets — before the team starts the day.
Analyze logs for IOCs from newly published threat reports, without re-querying each source manually.
Threat Hunting
An email in March and a malware case in July are often the same operator. Agents correlate across cases to surface campaigns that siloed teams miss.
Identify linkages between disparate malware or phishing incidents to surface broader campaigns your team missed.
Incident Response
Agents correlate logs across SIEM, endpoint, identity, and network telemetry into a single chronology — for the incident report, the regulator, or the post-incident review.
Correlate logs across tools to build a clear end-to-end attacker activity timeline — automatically.
Incident Response
Use Cases
Our AI agent serves as a junior cyber threat intelligence analyst, running investigations, enriching IOCs, and building threat actor profiles — so your team focuses on decisions, not data collection.
Use Cases
Supply chain intel
Your direct vendors are only the first layer. Agents profile the fourth and fifth parties your vendors depend on — the concentration risks, hidden dependencies, and adversarial exposures most programmes cannot see — using regulatory filings, automated scans, and open-source intelligence.
Supply Chain Intel
OSINT, dark web, and breach data are monitored against your vendor list. Active targeting surfaces before the compromise reaches your environment.
Social Media Intel
Agents map the hidden account networks, inauthentic amplification, and coordinated behaviour that shape narratives across social platforms. The operators behind the manipulated environment surface; the operation is named, not just its symptoms.
Social Media Intel
Agents cross-check identity documents, digital footprints, and behavioural signals to surface the fake personas, stolen credentials, and anomalous patterns that indicate a planted insider. The risk is caught before network access is granted — not after.
Financial Crime
Transactions in a bank statement are extracted, counterparties enriched, patterns identified, and an investigator-ready file produced. What used to take days takes minutes.
Financial Crime
Cross-domain correlation connects suspicious transactions to fake identities, known fraud infrastructure, and cyber signals. The organised scheme becomes visible, not just the symptom.
+ Trust & Readiness
Of the three layers that make enterprise AI deployable — foundational model, platform, and trust fabric — the trust fabric is the layer between raw model output and a decision your team can rely on. This is where the commitments below live.
Hallucination detection on every agent output. Drift detection across ongoing cases. Course-correction before conclusions reach the analyst review stage.
Every conclusion traces back to the sources and reasoning behind it. Every agent action is logged. Full audit logs across the platform.
ISO 27001 certified. SOC 2 Type II [achieved / in progress — state accurately]. Role-based access control and identity integration.
Investigation plans require analyst approval before execution. These were the conditions under which the product was built, not features added later.
Cloud, private GPU, or fully air-gapped on-premises — matched to sovereignty, classification, and operating constraints. Air-gapped is supported as a first-class configuration, not a workaround.
+ Differentiators
Threat intelligence platforms aggregate feeds. SOAR tools automate response playbooks. Neither runs the analysis that turns data into a conclusion. Protos AI is built for that work - the analytical and decision layer where the hard calls get made.
Anthropic, OpenAI, or bring your own. The LLM landscape will keep shifting. Your investment should not be stranded by it.
Every vendor platform now ships its own native agent — and each one sees only its own data. Real investigations cross feeds, tools, and vendor boundaries. Protos AI is the horizontal layer above your stack, not a slice within it.
Structured and unstructured. APIs, reports, logs, PDFs, statements, chats. Agents reason across all of it, surfacing connections the siloed tools never see.
EXPECTED OUTCOME
COST SAVING
Analyst time shifts from collection and pivoting to review and decision. Across every case, not only the high-priority few.
FASTER
From lots of data to a closed investigation in hours, not days. With full audit trail.
Optimize
Surface connections and adversary activity your team would otherwise miss — closing more investigations with the same headcount.
SPEED
Deploy, connect one data source, close a case. No multi-month implementation.
AWARDS & RECOGNITION
Backed by national cyber innovation programmes, global AI accelerators, and international security standards — proof our agentic AI meets the bar where it matters most.

Part of NVIDIA's accelerator for startups transforming industries through advances in AI and data science.

Selected for the AI Accelerate programme run by Block71, Microsoft and Enterprise Singapore — backing the next wave of AI-native startups.

Voted by attendees and powered by Thailand's National Cyber Security Agency — regional recognition from the cybersecurity community itself.

An earlier win under Singapore's national CyberCall programme — a track record of innovation recognised by CSA across multiple cycles.

Certified for information security management — the global benchmark for protecting customer data and systems.
SECTOR EXPERIENCE
Hands-on experience building AI for the defence and intelligence sector — where accuracy, security and trust are non-negotiable. The same rigour underpins every deployment of Protos AI.
TRUSTED BY OPERATORS
Used in operational environments where accuracy, speed, and trust are non-negotiable.
Across our cybersecurity engagements, the Protos Labs team has been responsive, technically strong, and easy to work with. They give us useful findings and practical explanations — not just data — which helps our members understand the risks and make informed decisions internally. Their reporting is clear and tailored for both technical and management audiences, and they’ve stayed proactive and collaborative throughout.
The Protos AI platform is intuitive and easy to use, and its customised cyber threat intelligence reports align perfectly with our operational requirements. We need fast, high-confidence sensing — and Protos AI consistently delivers. It has become deeply integrated into our daily workflows and plays a key role in our AI transformation, helping our teams act on actionable intelligence quickly and confidently.
GET IN TOUCH
Protos AI covers Cyber Threat, Financial Crime, and Supply Chain Risk — with unlimited investigations, custom integrations, collaboration across the team, priority support, and enterprise security.
Talk to SalesUnlimited investigations, custom integrations, team collaboration, priority support, and enterprise-grade security. Scale from analyst to SOC without switching tools.
Agentic AI is transforming how investigation teams operate. As an early partner, you'll help shape how intelligence and risk work evolves for tomorrow.