A walkthrough of the platform, in the order a team actually uses it. Configure an agent, connect your integrations, align workflows to your playbooks, run investigations on-demand or scheduled, review the output, build the knowledge graph, check the audit trail.
Every investigation on Protos AI is auditable by default, and every agent operates with a human in the loop. Both are requirements carried over from the environments the product was first built for.
Active agents, open investigations, hours saved, and cost per investigation — visible on one screen. When the head of CTI is asked what the team closed this month, the answer is already there.
Investigations completed, analyst hours saved, cost per investigation. Live.
Active agents, their case load, their completion rate.
Active, recent, and scheduled work. Owner, agent, and status, all visible.
A phishing triage agent. A fraud typology agent. A vulnerability hunt agent. Each shaped to the work, the tone, and the tools the team already uses. Four steps, no code.
Name the agent, define its purpose, assign it to a workflow.
Set tone, output format, and severity framing to match existing analyst playbooks.
Equip the agent with what it needs. OSINT, SIEM queries, graph building, reporting. Nothing extra.
Protos AI integrates with commercial intelligence feeds, government advisory channels, social media, and curated open-source channels — centralizing your data into a single, unified investigation workspace.
We support multiple formats such as API, STIX/TAXII, MCP, JSON, CSV, PDF and more.
Every investigation the team runs is preserved — the evidence, the reasoning, the conclusion. Ready for the regulator, the auditor, or the post-incident review, because in the environments Protos AI was built for, that readiness was not optional.
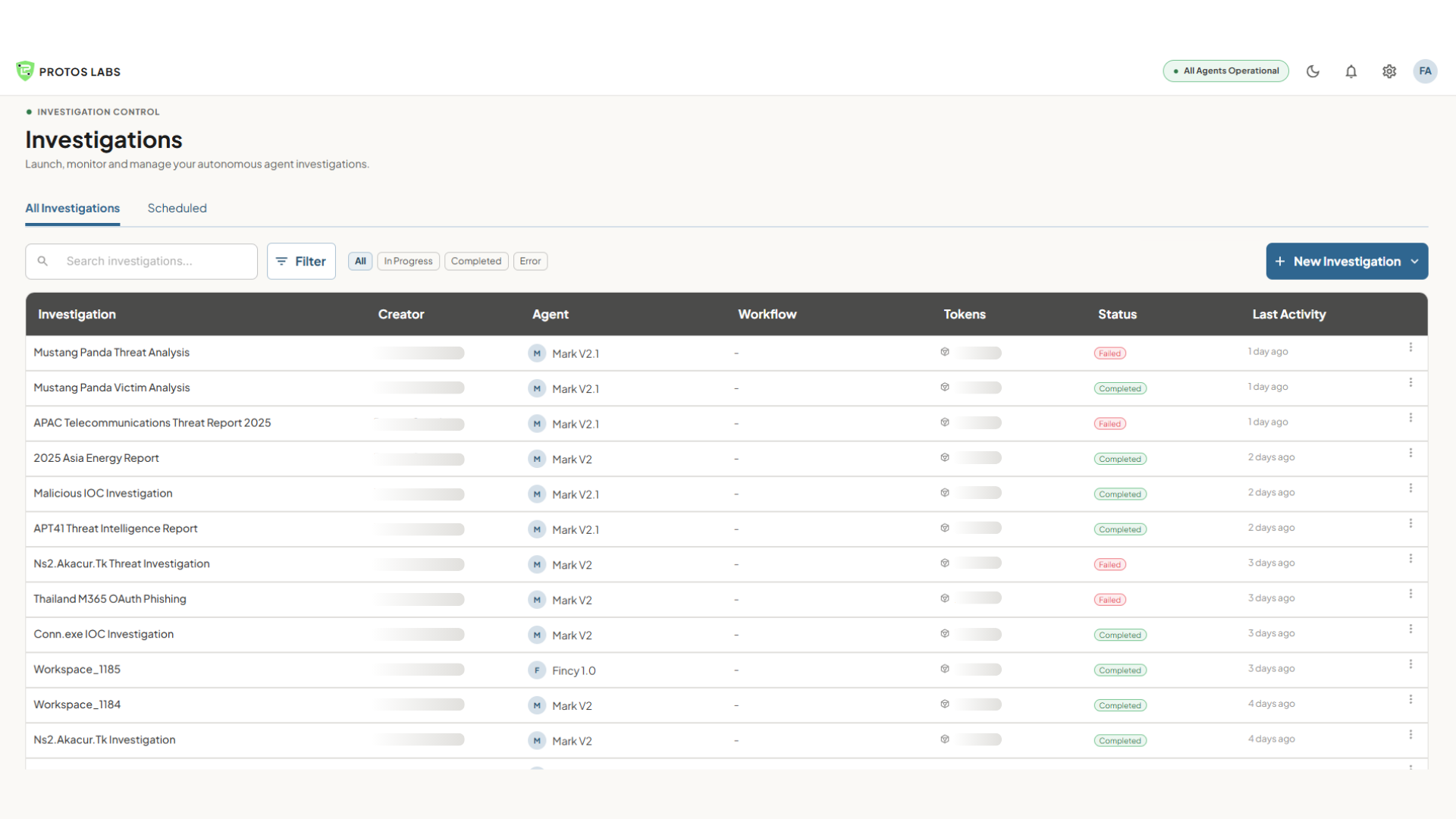
Every investigation, every agent, every outcome. Searchable, filterable, exportable.
Active, complete, awaiting review. Owner and assigned agent.
Token consumption per investigation, so cost per investigation is a number you can see, not a number you infer.
A three-column view. The sources the agent is drawing on. The chat where the analyst directs the work. The insights the agent is producing. A review step at the top, so nothing is promoted until the analyst signs off.
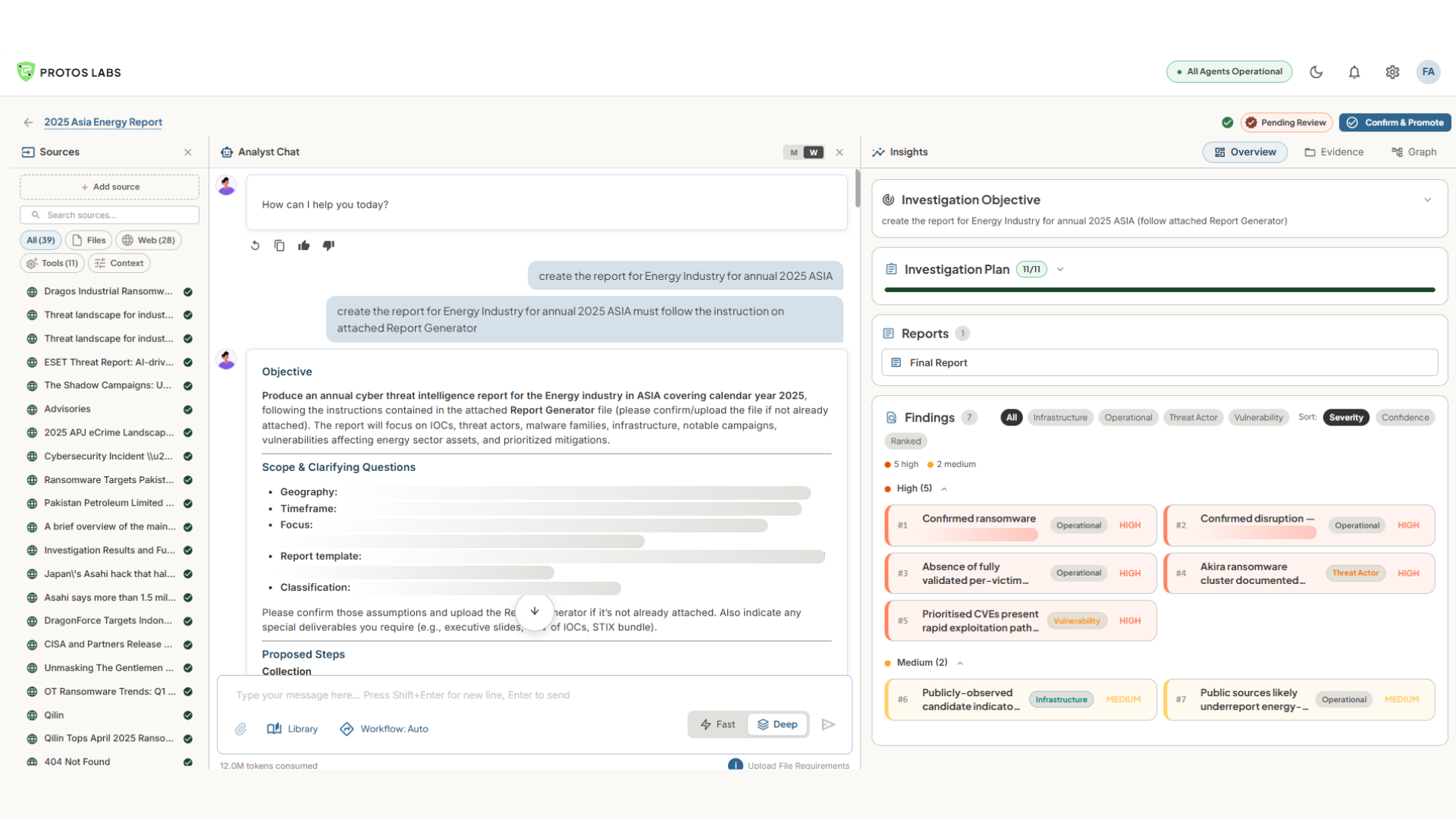
Every file, feed, and tool the agent is pulling from — visible, searchable, and individually verifiable. The analyst can see what the agent is working with, add a source mid-investigation, or exclude one that is not appropriate.
The conversation between the analyst and the agent. Objective, clarifying questions, proposed steps, and back-and-forth as the work progresses. A Fast or Deep mode, depending on whether the analyst wants a quick answer or a thorough one.
The structured output the agent is building — the objective as interpreted, the investigation plan with progress tracked, the findings ranked by severity, and the draft report. Overview, Evidence, and Graph views, depending on how the analyst wants to see it.
Findings sit in a Pending Review state until the analyst reviews them. Nothing is promoted to the AI's memory without that sign-off.
The Overview panel shows the investigation objective, a step-by-step investigation plan with progress tracking, the final report, and structured findings sorted by severity.
The full investigation brief at the top — including the target (KONNI APT), scope (deep-dive analysis), and specific deliverables requested.
A 7-step plan with real-time progress tracking (1/7 complete). Each step maps to a subagent phase: collection, analysis, graph building, reporting.
Structured findings sorted by severity (High/Medium/Low) with category tags — Threat Actor, Infrastructure, Operational — for immediate triage.
Most tools produce reports that are read once and filed. Protos AI builds a graph. Every entity, every relationship, every conclusion — carried forward across every investigation the team has run.
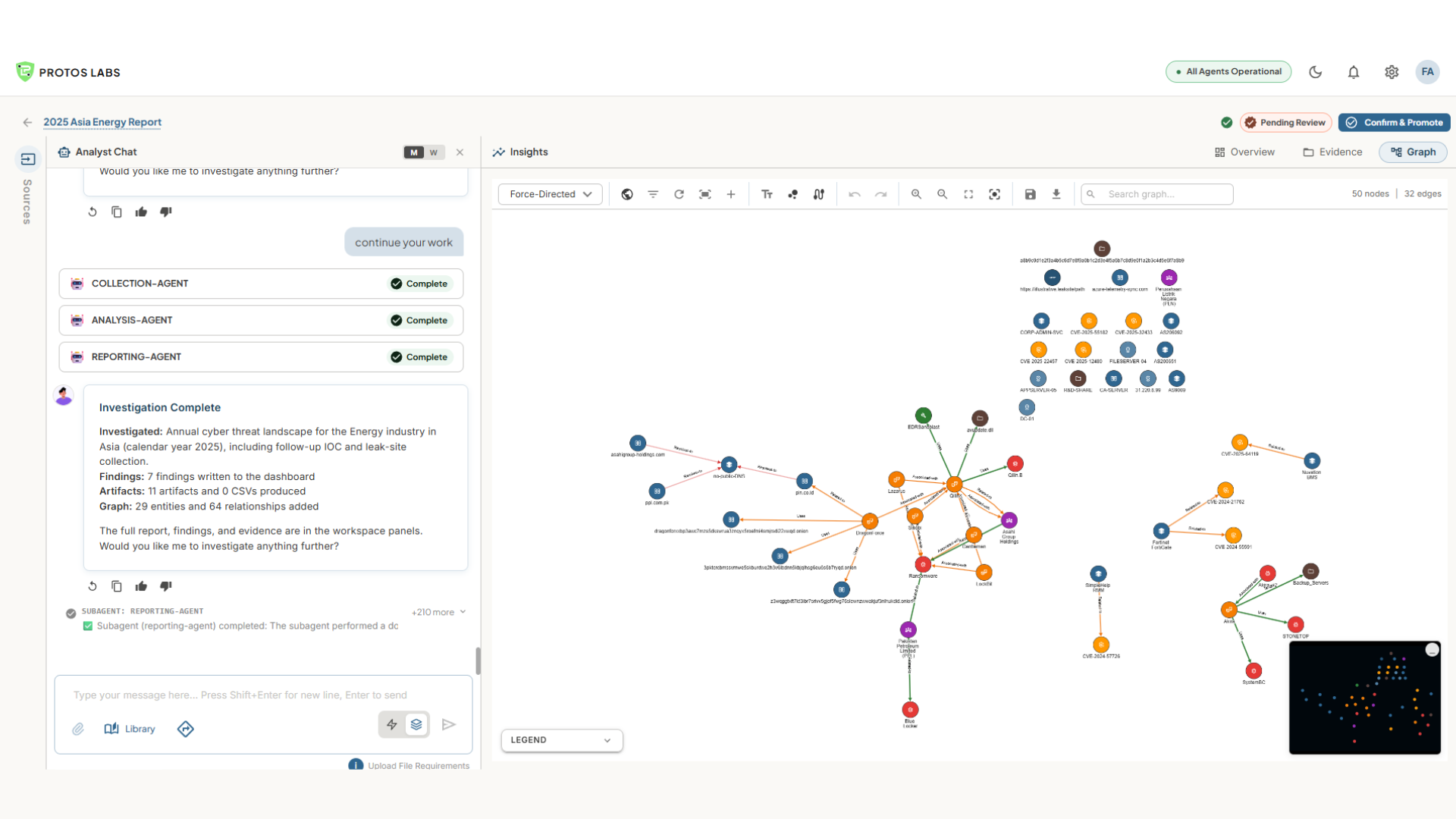
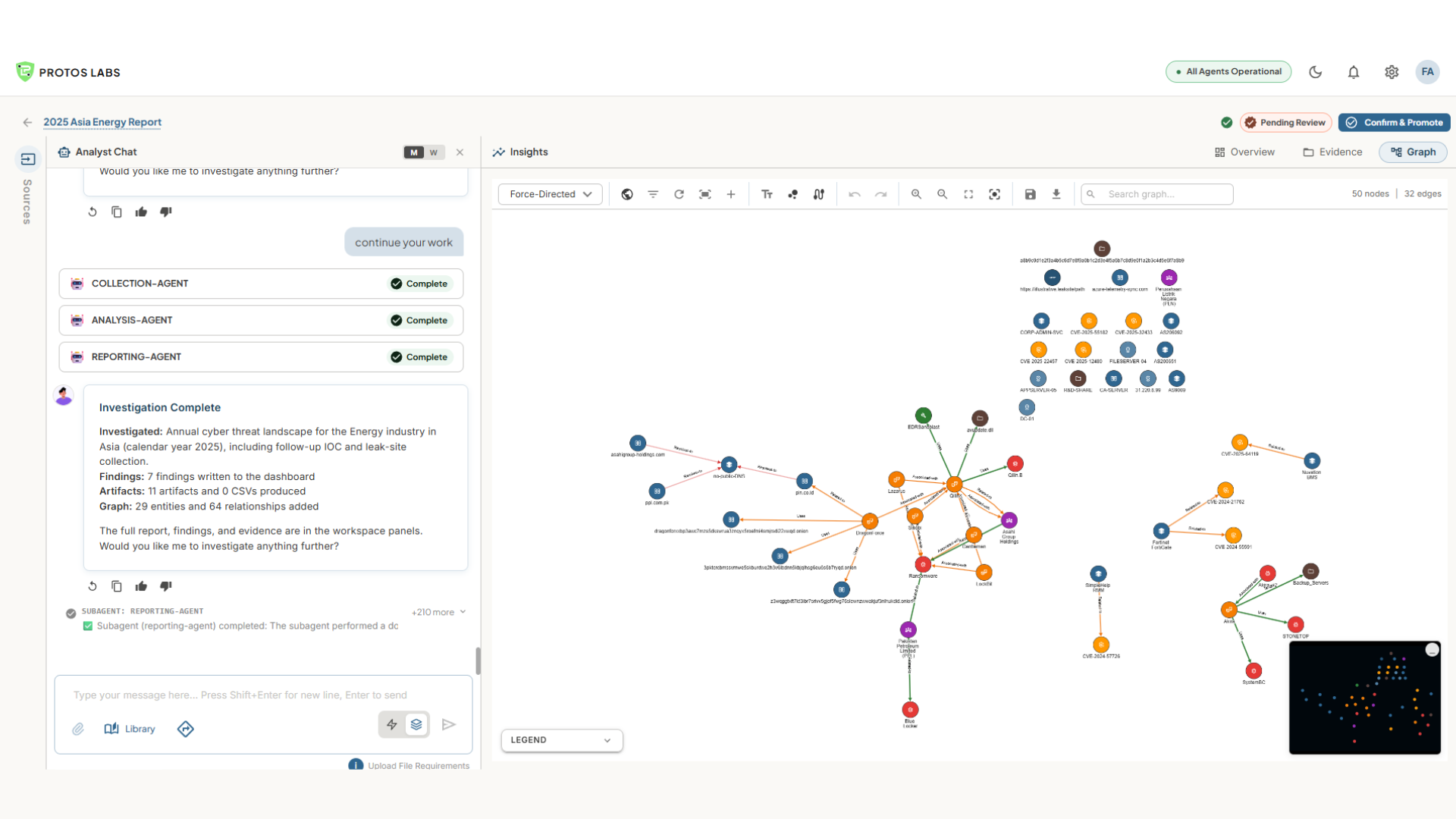

IP addresses, domains, malware, actors, vendors, identities. Extracted automatically, deduplicated, confidence-scored.
Every node carries its evidence and its confidence. No opaque attribution. Manually adjust the confidence to promote it to memory.
Campaign clusters, shared infrastructure, recurring techniques — visible across investigations, analysts, and time.
Every mature team has playbooks. The IOC enrichment sequence. The fraud escalation flow. The vendor compromise response. Protos AI runs them — step by step, with the team's customisations intact.
Word, Confluence, Jira. Parsed into executable workflows.
No code. No data science team required.
Tools, instructions, approval gates. The playbook remains the specification.
Free access to the cyber agent, with open-source intelligence and the full agent capability. Sample the product before any broader conversation.
Learn what Protos AI comes with below.
★ Compare TIERS
Pick the tier that fits where you are today. Upgrade when you need to scale.
Freemium
No credit card required
For individual analysts who want to start running AI-powered investigations immediately — no setup, no time limit.
✓
✓
✓
✓
✓
✓
✓
✓
First investigation brief in under 1 hour
Enterprise
Custom pricing based on team size & usage
For teams running investigations at scale — with commercial data feeds, third-party integrations, multi-user workspaces, dedicated infrastructure, and full platform control.
✓
✓
✓
✓
✓
✓
✓
✓
✓
We respond within 1 business day
| Capability | Freemium | Enterprise |
|---|---|---|
| Usage & Investigations | ||
| Primary use caseWhat this plan is built for | Individual investigations | Shared investigations & team workspace |
| Users | Single user | Multi-user teams |
| Token usageMonthly AI compute budget | Limited monthly tokens | ~20× higher token capacity |
| Data Sources & Integrations | ||
| Intelligence sourcesData feeds queried per investigation | OSINT & public intelligence sources | OSINT + commercial feeds + enterprise tool integrations |
| Workflow customization | Basic workflow templates | Custom investigation workflows |
| API accessProgrammatic platform access | — | Full API access |
| AI Model & Agent Capabilities | ||
| Model supportLLM powering investigations | Default model | Multi-LLM support |
| Bring Your Own Model / API Keys | — | Supported |
| AI skills & agent customizationCustom agent logic and skill sets | — | Custom AI skills and agents |
| Infrastructure & Security | ||
| Environment | Shared platform | Dedicated environment |
| Data isolation | Shared environment | Dedicated data isolation |
| Security & access control | Basic authentication | Enterprise RBAC & identity integration |
| Audit trail | — | Full investigation audit logs |
| Reporting & Support | ||
| Investigation reporting | Standard investigation reports | Customizable intelligence reports |
| Support | Community / basic | Dedicated support |