Adversarial Risk Intelligence PlatforM
Across cyber, fraud, and supply chain — AI that investigates adversarial activity 15× faster and tells you what it means for your organisation. Conclusions, not alerts.
+ INDUSTRIES WE SERVE
✦ PROBLEM
Attacks are coming faster and from more directions than ever. AI-powered attacks now add to the non-AI attacks that were already overwhelming defenders. Adversaries attack at machine speed. Defenders still investigate at human speed. That gap is where breaches happen.
The people who can properly investigate complex threats are hard to hire, harder to keep, and take their hard-won knowledge with them when they leave.
Your SIEM, transaction monitoring, and third-party risk systems already bring the data together. The bottleneck now is the human analysis that turns that data into a conclusion — investigation by investigation, analyst by analyst, domain by domain.
Advisories, reports, and alerts arrive in real time. Working out what they mean for your specific environment — your assets, your counterparties, your exposures — still takes hours of manual analysis. By the time that analysis finishes, the adversary has already moved on.
+ SOLUTION
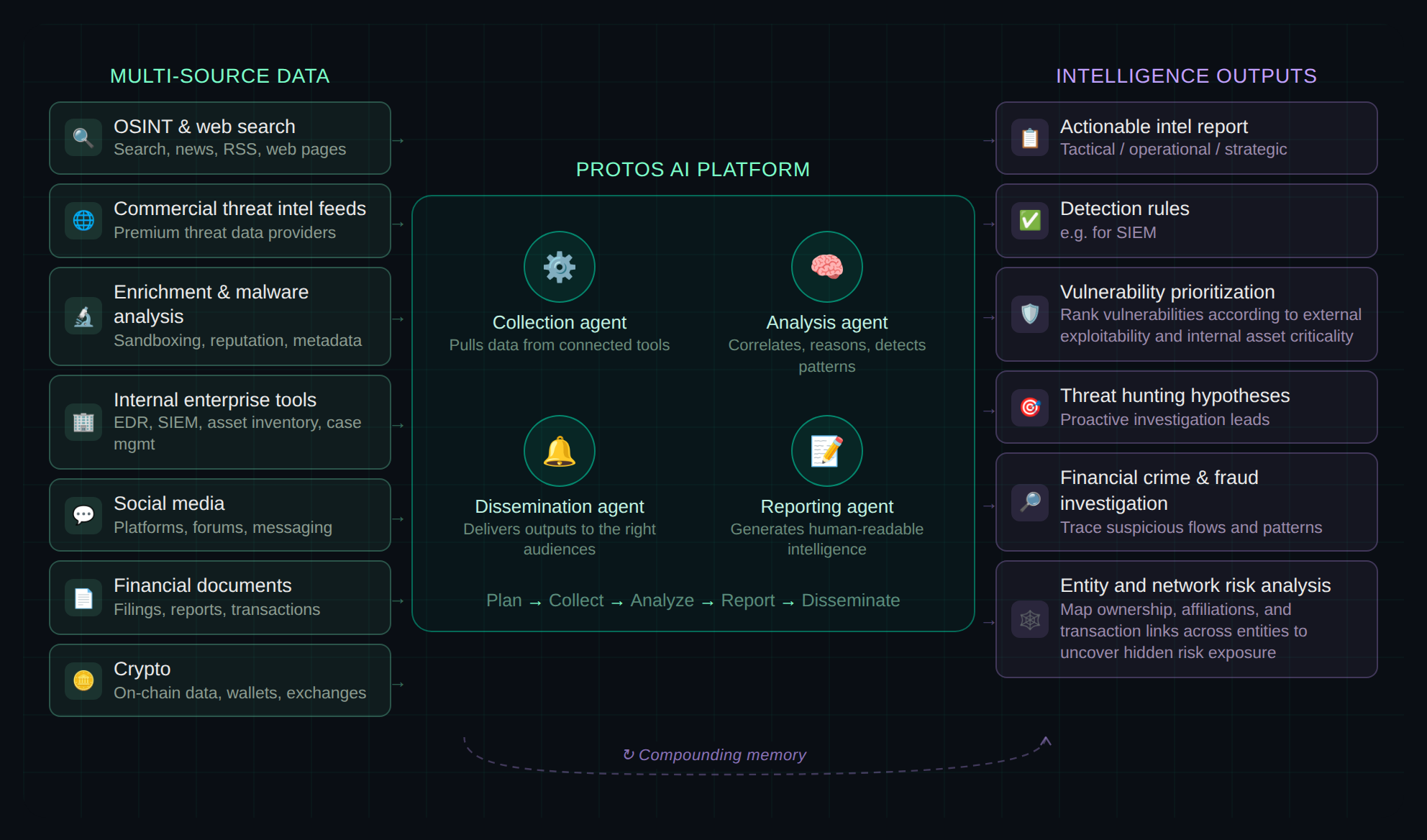
Protos AI is the intelligence layer for investigation teams. Our AI agents investigate across every place adversaries operate — your enterprise systems, the open web, social media, and the dark corners of the internet — then translate what they find into what it means for your organisation. Not enriched indicators. Conclusions your team can act on.
+ The PROTOS Advantage
Most platforms treat each investigation as a one-off output. We treat it as a contribution to a system that gets smarter, broader, and more accurate with every case
Every investigation teaches the next. Our AI agents build a persistent memory of your environment, your adversaries, and your past work — so your 1,000th case is exponentially more informed than your first.
Specialised agents investigate across cyber, fraud, supply chain, and other adversarial risk domains — connecting activity no single tool can see alone. Threats don't respect departmental boundaries. Neither do your agents.
When one organisation's agents discover a new adversary pattern, every participant's defences get stronger. A living network where shared intelligence creates shared defence.
The adversary is the unit of analysis, not the alert.
+ USE CASES
+ USE CASES
Our AI agent serves as a junior cyber threat intelligence analyst — delivering across core CTI use cases, autonomously and at scale.
Autonomously enrich indicators, map MITRE ATT&CK techniques, and analyze supporting infrastructure — eliminating manual lookups.
Continuously monitor vendors for active targeting. Protect vendors without in-house CTI capabilities.
Identify CVEs from threat advisories and map to impacted assets. Automate regulatory advisory responses.
Analyze logs for IOCs from newly published threat reports. Parse raw logs, flag malicious behavior against known threats.
Identify linkages between disparate malware or phishing incidents. Deep link analysis uncovering hidden cross-campaign connections.
Correlate logs across tools to build a clear end-to-end attacker activity timeline — no manual console switching.
+ USE CASES
Our AI agent serves as a junior investigation analyst — delivering use cases across cyber insurance, financial crime, trade compliance and risk intelligence.
CYBER INSURANCE
Cross-validate proposal forms, underwriting guidelines and attack surface scans for better risk decisions.
CYBER INSURANCE
Scan your insurance portfolio to detect exposure to a new vulnerability. What took days, now takes minutes.
FINANCIAL CRIME
Reduce false positives by prioritising alerts based on behavioural risk, materiality, and context.
FINANCIAL CRIME
Identify emerging fraud patterns and control gaps by analysing confirmed fraud cases and transaction behaviour.
TRADE COMPLIANCE
Improve sanctions decisions by contextualising counterparties, transactions, and jurisdictions against true compliance risk.
COMPLIANCE
Accelerate onboarding by synthesising vendor data, intelligence and risk signals into clear, defensible assessments.
Protos AI applies human-analyst-level tradecraft to every investigation.
Use Cases
Autonomously enrich indicators, map MITRE ATT&CK techniques, and build actor-linked correlation graphs — without manual pivoting.
Autonomously enrich indicators, map MITRE ATT&CK techniques, and build actor-linked correlation graphs — without manual pivoting.
Threat Intel
Automatically investigate reported phishing emails and suspicious domains — analysing registration patterns, hosting infrastructure, and actor attribution across every alert.
Continuously monitor vendors for active targeting, exposure events, and threat actor mentions across OSINT, dark web, and breach feeds.
Threat Intel
Correlate threat advisories with active exploitation activity and adversary campaigns — prioritising CVEs your attackers are actually weaponising, mapped to your exposed assets.
Identify CVEs from threat advisories and map to impacted assets in your environment, with EPSS-driven prioritisation.
Vulnerability Management
Sweep historical logs for newly disclosed IOCs, TTPs, and threat actor signatures — uncovering past adversary activity that bypassed your defences the first time around.
Analyze logs for IOCs from newly published threat reports, without re-querying each source manually.
Threat Hunting
Identify linkages between disparate malware or phishing incidents to surface broader campaigns your team missed.
Identify linkages between disparate malware or phishing incidents to surface broader campaigns your team missed.
Incident Response
Correlate logs across tools to build a clear end-to-end attacker activity timeline — automatically.
Correlate logs across tools to build a clear end-to-end attacker activity timeline — automatically.
Incident Response
Use Cases
Our AI agent serves as a junior cyber threat intelligence analyst, running investigations, enriching IOCs, and building threat actor profiles — so your team focuses on decisions, not data collection.
Use Cases
Supply chain intel
Map your supply chain beyond direct vendors — uncovering concentration risk, hidden dependencies, and adversarial exposure two to three layers deep through regulatory filings, automated scans, and open-source intelligence.
Supply Chain Intel
Monitor vendors and third parties for active threat actor targeting, breach indicators, and dark web exposure — catching compromised partners before the breach cascades into your environment.
Social Media Intel
Map coordinated campaigns and hidden account networks shaping narratives across social platforms - surfacing hidden operators behind manipulated environments.
Social Media Intel
Detect fake identities, suspicious credentials, and anomalous footprints among contractors and remote workers — before they gain access to your systems.
Financial Crime
Enrich transactions with entity profiles, known fraud patterns, and dark web intelligence to accelerate investigations.
Financial Crime
Investigate fraud schemes beyond transactions — correlating behavioural, identity, cyber, and open-source signals to surface the hidden networks, fake personas, and infrastructure behind each case.
+ OUR Differentiators
Protos AI is engineered for immediate performance, adaptability and accountability.
Built to meet the security, compliance, and uptime standards your organization demands — ready for production from day one.
Not locked into any single AI model. As the LLM landscape evolves, Protos AI adopts the best-performing models over time — protecting your investment and ensuring continuous improvement.
Correlates horizontally across all your data sources — threat feeds, enrichment tools, transaction systems, and enterprise data. No ecosystem lock-in — works with what you have.
Cloud-managed, private GPU, or on-premise air-gapped deployment. Matched to your data privacy, sovereignty, and cost requirements.
Built to meet the security and compliance standards your organisation demands. SOC2, ISO 27001, ready for production from day one.
EXPECTED OUTCOME
COST SAVING
Free analyst time through automated triage and enrichment across every case, not just the high-priority few
FASTER
From raw data to closed investigation in minutes, not hours or days — with full audit trail.
Optimize
Surface connections and adversary activity your team would otherwise miss — closing more investigations with the same headcount.
SPEED
Deploy, connect your first data source, and close your first investigation within seven days — no multi-quarter implementation
EXPERIENCE PROTOS AI
Run your first AI-powered cyber investigation using open-source intelligence. Enrich IOCs, map TTPs, and analyse threat actor infrastructure — experience Protos AI's agentic capabilities in minutes, no credit card required. Built for Cyber Threat Intelligence teams getting started with agentic AI. Not your typical AI SOC analyst.
Connect proprietary data sources, dark web feeds, OSINT investigation tools and unstructured files. Expand into financial crime, fraud, and cross-domain investigations with unlimited cases, team collaboration, priority support, and enterprise-grade security.
Contact SalesUnlimited investigations, custom integrations, team collaboration, priority support, and enterprise-grade security. Scale from analyst to SOC without switching tools.
Agentic AI is transforming how investigation teams operate. As an early partner, you'll help shape how intelligence and risk work evolves for tomorrow.