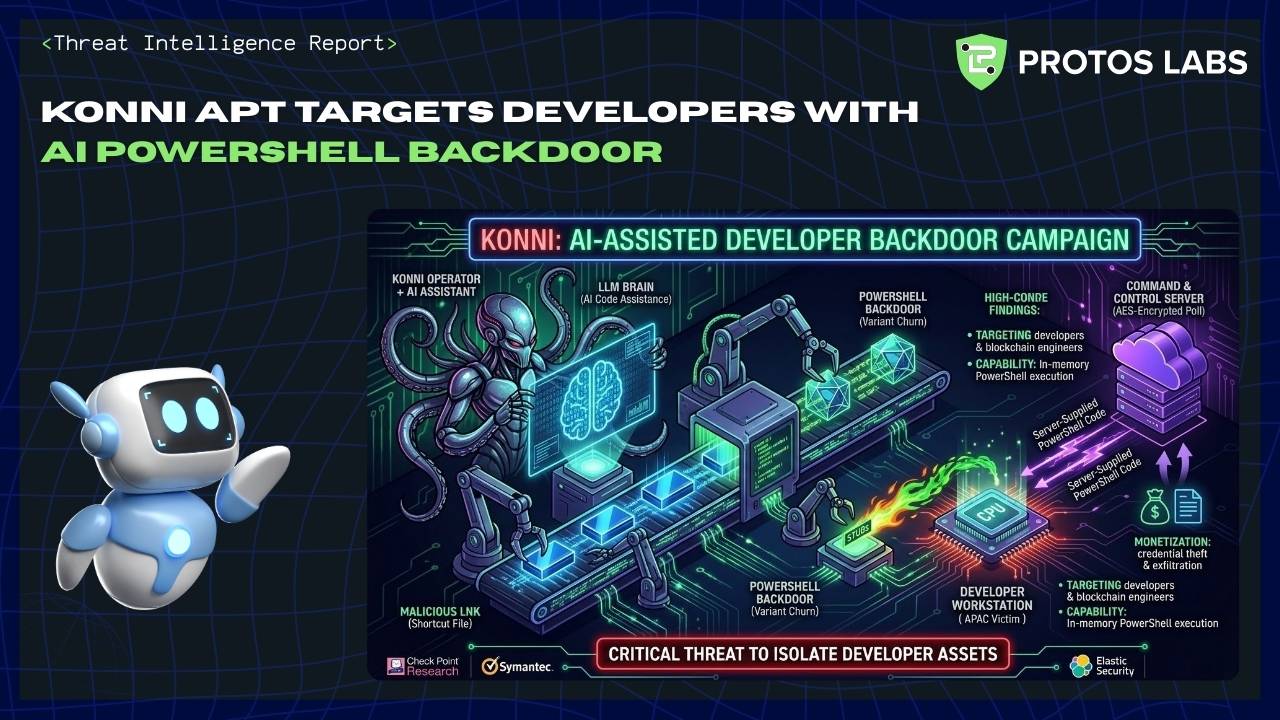
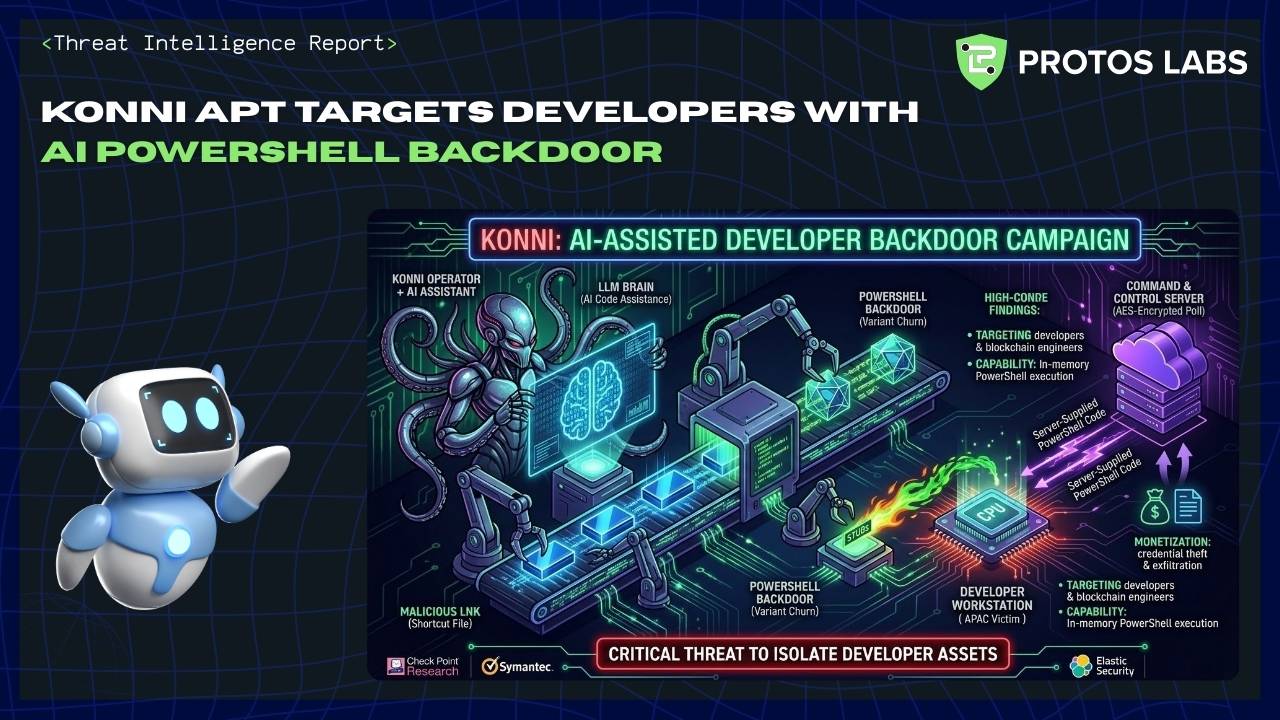
KONNI APT Targets Developers With AI PowerShell Backdoor
Protos AI CTI Agent V 2.1
Protos AI CTI Agent V 2.1
| Classification | Date | Risk Level | Confidence |
|---|---|---|---|
| TLP:CLEAR | 2026-03-04 | HIGH | Medium–High |
| Attribute | Value |
|---|---|
| Risk Level | HIGH |
| Confidence | Medium–High |
| Key Finding | KONNI conducted a developer-targeting phishing campaign in January 2026 that delivered an AI-assisted PowerShell backdoor enabling encrypted C2 and in-memory execution. |
| Primary Action | Immediate: Hunt for scheduled tasks invoking obfuscated PowerShell and block identified malicious hashes and C2 endpoints after telemetry validation. |
Available vendor reporting indicates a January 2026 campaign that prioritized developer personas (including blockchain engineers) and delivered a PowerShell backdoor that executed server-supplied code in memory and used encrypted C2.
Detection should prioritize behavioral indicators (LNK → PowerShell → XOR-decrypt → IEX; scheduled tasks; AES-protected C2) over static signatures due to likely variant churn. C4
| Scope Item | Details |
|---|---|
| Investigation Focus | KONNI January 2026 campaign: delivery chain, malware capabilities, infrastructure, TTPs, IOCs, and evolution |
| Time Period | January 2026 (primary); historical baseline 2019–2025 |
| Sources Used | Threat intelligence reporting, vendor technical analyses, OSINT research, artifact-level sample analysis |
| Methodology | Reviewed vendor technical writeups; mapped behavior to ATT&CK; assessed attribution and evolution vs. historical KONNI reporting |
The January 2026 operation prioritized developers (including blockchain engineers) to access high-value credentials and project secrets.
Evidence: Check Point and supporting vendor reporting describe developer-oriented lures and delivery channels.
Analysis: Developer-targeted lures materially increase exposure to source code, CI/CD tokens, and environment secrets. C6
The backdoor uses AES-style encrypted command channels and executes server-supplied PowerShell code entirely in memory.
Evidence: Technical sample analysis demonstrating AES protection and IEX in-memory execution.
Analysis: Encrypted C2 and in-memory execution reduce opportunity for static detection. C4
| # | Finding | Evidence | Caveat |
|---|---|---|---|
| 1 | Delivery chain: collaboration platform → ZIP → LNK → PowerShell loader | Vendor technical walkthroughs documenting ZIP+LNK delivery. | Validate platform-specific URLs; the platform itself is not an IOC. |
| 2 | Persistence & anti-analysis — scheduled tasks, UUID single-instance enforcement | Sample analysis and vendor reports. C3 | Patterns may vary across variants. |
| 3 | Attribution to KONNI — TTP overlap and launcher reuse | Check Point IOC lists; multiple vendor attribution. | Evidence-based but not definitive — operator mimicry remains a possibility. |
Vendor reports published sample hashes and listed domains/IPs. Hash listings should be validated against internal telemetry before blocking. C7
| Vertex | Findings | Confidence |
|---|---|---|
| Adversary | KONNI (North Korea–linked cluster) — vendor attribution present but not incontrovertible | Medium |
| Capability | PowerShell backdoor with encrypted C2, anti-analysis, in-memory code execution | High |
| Infrastructure | Public file-sharing delivery channel; vendor-listed domains/IPs and sample hashes (needs validation) | Medium |
| Victim | Software developers (incl. blockchain engineers) in APAC & beyond | High |
| Stage | Evidence | Status |
|---|---|---|
| Reconnaissance | Developer project materials used as lures | Observed |
| Delivery | Collaboration/file-sharing link → ZIP with LNK C2 | Observed |
| Exploitation | LNK launched PowerShell loader (user interaction) | Observed |
| Installation | Scheduled task persistence; occasional service/RMM install C5 | Observed |
| Command & Control | Encrypted polling and server-supplied PowerShell C4 | Observed |
| Actions on Objectives | Staged upload/exfiltration workflows observed in samples C4 | Observed |
Summary: January 2026 retains KONNI's established multi-stage phishing and encrypted C2 approach but shows two notable shifts: explicit developer-centric targeting and introduction of AI-assisted/LLM-style code artifacts.
| Dimension | Detail | Citation |
|---|---|---|
| Continuities | Social engineering → multi-stage loader → persistence → encrypted C2; UAC bypass and staged uploads consistent with historical KONNI. | C8 |
| Evolutions | Targeting shifted to developer communities; code artifacts exhibit LLM-style structure consistent with AI assistance — may increase variant churn. | C9 |
| # | Action | Rationale | Owner |
|---|---|---|---|
| 1 | Hunt & remediate: Search for scheduled tasks invoking PowerShell with XOR/IEX strings; isolate and rotate credentials if found. | Matches observed persistence + in-memory execution. | IR / EDR Team |
| 2 | Block & validate: Ingest vendor SHA256 hashes into quarantine after validating against internal telemetry. | Vendor-published hashes map to observed ZIP/LNK samples. | Threat Intel / SOC |
| 3 | Restrict LNK → PowerShell: Block shortcuts launching PowerShell from user-download folders. | Prevents the primary observed delivery chain. | Endpoint / SOC |
| # | Action | Rationale |
|---|---|---|
| 1 | Harden developer secrets: Enforce short-lived tokens, remove long-lived credentials, mandate vaulting. | Limits post-compromise value of developer hosts. |
| 2 | Network detection: Create signatures for AES-wrapped C2, /api/errorMessage-like endpoints, anomalous POST/GET patterns. | Detects encrypted C2 and exfiltration behaviors. |
f7d77a6d-36e0-4fcb-bae7-5f4b3b723f61 (defanged). C3| Type | Indicator | Context | Risk |
|---|---|---|---|
| Domain | filetrasfer[.]wuaze[.]com | Domain observed in vendor IOC lists (validate before blocking). | MEDIUM |
| Domain | price-oracle-v2[.]vercel[.]app | Developer-style staging domain in vendor reporting (validate). | MEDIUM |
| IP | 87[.]236[.]177[.]9 | Reported stage 2 C2 host (validate in your network before blocking). | MEDIUM |
| Type | Hash / Value | Filename | Context |
|---|---|---|---|
| SHA256 | c79ef378...ade5d5 | (ZIP sample) | Published vendor hash — confirmed in vendor IOC list. C7 |
| SHA256 | 39fdff2e...1760c | (LNK launcher) | Published vendor hash — confirmed in vendor IOC list. C7 |
| Filename | OneDriveUpdate.ps1 / schedule1.bat / simi.bat | Staging filenames | Observed in samples. Observable. |
| Mutex/UUID | f7d77a6d-36e0-4fcb-bae7-5f4b3b723f61 | — | Hardcoded UUID for single-instance enforcement (huntable). HIGH C3 |
Analysis relies on vendor-published sample analyses and reporting; internal telemetry was not available in this investigation.
| Confidence Level | Findings |
|---|---|
| High | Developer targeting (Key Finding 1); Encrypted C2 & in-memory execution (Key Finding 2) |
| Medium | Delivery chain details; Persistence & anti-analysis; Vendor attribution to KONNI; AI-assistance assessment |
| Low/Unverified | Some infrastructure domains and hosting relationships pending validation in internal telemetry |
| Source Type | Description |
|---|---|
| Threat Intelligence | Check Point Research, Broadcom/Symantec protection bulletin, vendor sample analyses (primary) |
| OSINT Research | Secondary press and vendor summarizations (DarkReading, BleepingComputer) |
| Historical Analysis | Fortinet/FortiGuard Labs KONNI baseline reporting (historic TTP comparison) |
Protos AI automates CTI investigations using agentic AI — from OSINT collection to structured analysis. Speak to our team to see it in action.