TLP:CLEAR
|
Analyst: Protos AI Threat Intelligence
At-a-Glance
| Attribute | Value |
|---|
| Risk Level | HIGH |
| Confidence | MEDIUM-HIGH |
| Threat Actor | Handala (Iranian-linked) |
| Target | Stryker Corporation — Medical device manufacturer |
| Incident Date | 11 March 2026 |
| Attack Type | Destructive / Wiper — likely hybrid (malware + admin control-plane abuse) |
| Key Finding | Mass device wipe disrupted Stryker's internal Microsoft environment; plausible Intune remote-wipe abuse identified as contributing mechanism |
| Primary Action | Enforce multi-admin approval for bulk remote-wipe; harden identity/MDM privilege; deploy mass-wipe detections |
Executive Summary
Stryker Corporation publicly disclosed a cyber incident on 2026-03-11 that disrupted corporate Microsoft services and impacted employee access to corporate systems. Multiple independent reports indicate employee devices were remotely wiped or rendered unusable during the disruption window.
Public vendor reporting and actor messaging attribute the event to Handala; however, available public evidence does not include victim-validated forensic IOCs. Most concrete indicators are vendor-sourced or actor-published and should be used for hunting and correlation rather than immediate enforcement.
Key Finding
The event is best characterised as a likely hybrid destructive attack — including plausible abuse of administrative control planes (e.g., Microsoft Intune remote wipe) rather than conclusively malware-only. This distinction is critical for defensive prioritisation.
Primary Action
Prioritise identity and MDM privilege hardening, enforce multi-admin approvals for destructive admin actions, and deploy detection logic for mass remote-wipe activity across managed device fleets.
Investigation Scope & Methodology
| Scope Item | Details |
|---|
| Investigation Focus | Reconstruct the March 2026 Stryker/Handala attack timeline; identify defanged IOCs; map to MITRE ATT&CK; document unique insights |
| Time Period | March 2026 event window and ~30 days prior context |
| Sources Used | OSINT research, vendor threat intelligence reports, DNS analysis, internet scan results |
| Methodology | Reviewed structured claims, synthesised vendor research and OSINT, reconstructed timeline, mapped techniques to MITRE ATT&CK, extracted observables for contextual hunting |
Key Findings
High Confidence
| # | Finding | Risk |
|---|
| 1 |
A destructive incident occurred at Stryker on 2026-03-11 that materially disrupted the internal Microsoft environment and rendered many managed devices unusable. Supported by Stryker public disclosure and independent reports of remote wipes and device loss. |
HIGH |
| 2 |
Publicly available technical indicators are primarily vendor-sourced or actor-published and are not victim-validated. Best used for hunting and retrospective correlation — not immediate perimeter blocking. |
MEDIUM |
Medium Confidence
| # | Finding | Caveat |
|---|
| 1 |
Handala is the most plausible public attribution — but attribution remains primarily claim/context-based, not victim-forensic. |
Not victim-validated |
| 2 |
Microsoft Intune remote-wipe abuse is a plausible and likely contributing mechanism, but public evidence does not exclude parallel malware or scheduled-task-based destructive activity. |
No Intune audit logs in public sources |
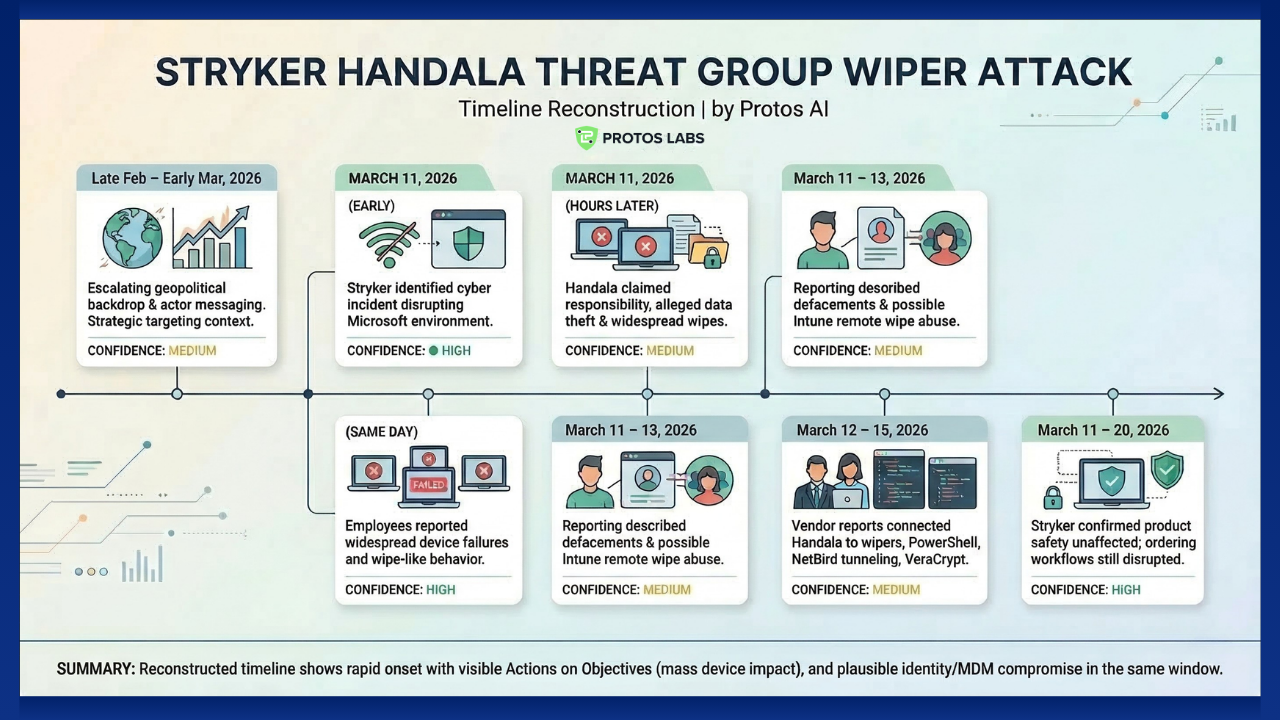
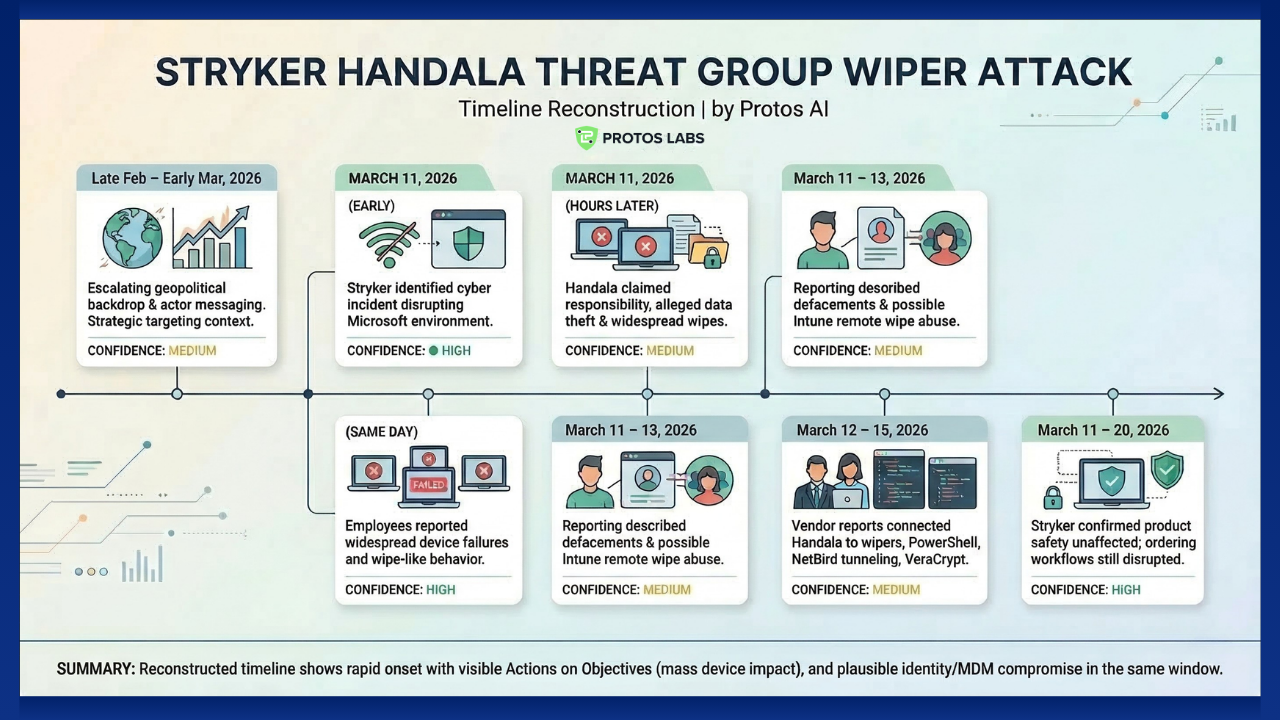
Attack Timeline Reconstruction
Late Feb – Early Mar 2026
Geopolitical backdrop and actor messaging escalated — strategic context for targeting established.
Confidence: MEDIUM
Stryker identified a cyber incident disrupting the internal Microsoft environment and corporate systems — verified victim-side milestone.
Confidence: HIGH
Employees reported widespread device failures and wipe-like behaviour. Rapid enterprise-scale impact observed across managed device fleet.
Confidence: HIGH
Handala published responsibility claims and alleged large-scale data theft and widespread wipes. Volumes remain unverified.
Confidence: MEDIUM
Reporting described Microsoft Entra-linked defacements and possible Intune remote-wipe abuse — suggests identity/MDM compromise amplified impact.
Confidence: MEDIUM
Vendor reports connected Handala to wipers, PowerShell destructive scripts, NetBird tunnelling, and VeraCrypt misuse. Actor tradecraft context — not Stryker-specific proof.
Confidence: MEDIUM
Stryker clarified product safety was unaffected; internal ordering workflows remained disrupted.
Confidence: HIGH
MITRE ATT&CK Mapping
| Tactic | Technique ID | Technique | Confidence |
|---|
| Initial Access | T1133 | External Remote Services — vendor reporting includes compromised remote access; not Stryker-confirmed. | LOW-MED |
| Credential Access | T1003.001 | OS Credential Dumping: LSASS Memory — reported in broader actor tradecraft; not Stryker-confirmed. | LOW-MED |
| Discovery | T1087.002 | Account Discovery: Domain Account — relevant if identity/MDM abuse occurred. | LOW-MED |
| Lateral Movement | T1021.001 | Remote Services: RDP — seen in vendor reporting for actor operations; not Stryker-validated. | LOW-MED |
| Defence Evasion | T1572 | Protocol Tunnelling — NetBird usage in vendor reporting supports tunnelling capabilities. | MEDIUM |
| Persistence / Execution | T1053.005 | Scheduled Task — vendor reports include scheduled tasks/GPO deployment in actor playbook. | LOW-MED |
| Impact | T1485 | Data Destruction — strong alignment with observed wipe-like effects at Stryker. | HIGH |
| Impact | T1561.001 / T1561.002 | Disk Wipe / Disk Structure Wipe — relevant to wiper tradecraft reported for Handala. | MEDIUM |
Infrastructure Analysis
| Indicator | Hosting / Notes | Key Observations |
|---|
handala-hack[.]to | Actor-hosted domain | Reported actor hosting for claims/screenshots; non-resolving at collection time. |
handala[.]to | Actor domain | Alternate actor-associated domain; non-resolving at collection time. |
31[.]57[.]35[.]223 | VPS/VPN candidate | Internet scan showed exposed Windows RPC/SMB — consistent with Windows-oriented operational infrastructure. |
82[.]25[.]35[.]25 | VPS/VPN candidate | Internet scan showed exposed Windows RPC/SMB — treat as contextual. |
146[.]185[.]219[.]235 | VPN/exit node candidate | Vendor-cited VPN exit node; likely shared hosting infrastructure. |
Indicators of Compromise (All Defanged)
Network Indicators
Domain
handala-hack[.]to
Actor claim/propaganda hosting; non-resolving at collection time.
MEDIUM
Domain
handala[.]to
Alternate actor domain; non-resolving at collection time.
MEDIUM
URL
t[.]me/HANDALA_HPR2
Actor Telegram channel used for claims and messaging.
MEDIUM
IP
107[.]189[.]19[.]52
Vendor-associated infrastructure; no public scan confirmation.
MEDIUM
IP
31[.]57[.]35[.]223
Vendor-cited IP with exposed RPC/SMB services; contextual candidate.
MEDIUM
IP
82[.]25[.]35[.]25
Vendor-cited IP with exposed RPC/SMB services; contextual candidate.
MEDIUM
IP
146[.]185[.]219[.]235
Vendor-cited VPN/exit node candidate; likely shared infrastructure.
LOW
File Indicators — Vendor-Reported, Not Victim-Validated
SHA256
5986ab04dd6b3d259935249741d3eff2
Reported Handala wiper sample.
MEDIUM
MD5
3cb9dea916432ffb8784ac36d1f2d3cd
Reported PowerShell wiper sample.
MEDIUM
SHA256
3236facc7a30df4ba4e57fddfba41ec5
VeraCrypt installer — dual-use tooling; context required before blocking.
LOW
SHA256
3dfb151d082df7937b01e2bb6030fe4a
NetBird installer — dual-use tunnelling tool; detect via context, not name.
LOW
Analytic note: IOCs are vendor-sourced or actor-published. Use for hunting, retrospective correlation, and enrichment. Operational blocking should require victim telemetry or higher-confidence confirmation.
Risk Assessment
| Risk Factor | Rating | Justification |
|---|
| Threat Sophistication | MED-HIGH | Actor demonstrates destructive tradecraft, propaganda capability, and effective use of dual-use tooling. |
| Potential Impact | HIGH | Rapid enterprise-scale device impact observed; significant disruption to internal ordering and corporate workflows. |
| Likelihood of Exploitation | MED-HIGH | Attack achieved visible impact; identity/MDM abuse increases feasibility of mass disruption for similar organisations. |
| Overall Risk | HIGH | Combined impact severity, actor capability, and plausible administrative-plane abuse produce a high systemic risk rating. |
Recommendations & Mitigation
Priority 1 — Immediate Actions
Action 1
Enforce multi-admin approval and break-glass controls for bulk remote-wipe actions
Require step-up authentication for any bulk device retire, reset, or wipe commands in Microsoft Intune. Prevents single-point administrative misuse from causing enterprise-wide device loss.
Owner: Identity / Platform Team
Action 2
Rotate and audit all privileged credentials for identity and MDM administration
Enable Conditional Access and restrict privileged admin sign-ins by location and device posture. Limits attacker ability to abuse identity-plane controls for destructive actions.
Owner: Identity / IT
Action 3
Isolate and recover impacted device groups via secure offline process
Perform offline forensic capture prior to wide re-imaging where possible. Preserves evidence and reduces the risk of reinfection or a repeated destructive wipe.
Owner: Incident Response
Priority 2 — Short-term Actions
Action 1
Deploy detections for mass remote-wipe and anomalous Intune admin activity
Correlate Intune/MDM admin commands with device check-ins, unusual timing, and admin session geolocations. Alert on bulk retire/reset activity, sudden privilege escalation, or step-ups from new IP ranges.
Action 2
Conduct hunts using vendor-published observables
Search for the network and file IOCs in this report across logs from the incident window. Require victim telemetry before converting to enforcement rules.
Priority 3 — Long-term Improvements
Harden privileged access with JIT/JEA models and out-of-band approval workflows
Implement Just-In-Time and Just-Enough-Administration models for device management. Test recovery playbooks that assume simultaneous loss of endpoints and identity-plane access. Improve logging retention and centralisation for MDM platforms to enable faster forensic reconstruction.
Unique Insights
Insight 1
Destructive impact without a malware-heavy footprint
The Stryker event demonstrates that administrative control-plane abuse (e.g., Intune remote wipe) can produce mass wipe-like outcomes without widespread malware detections — fundamentally challenging EDR-centric defensive assumptions.
Insight 2
Administrative trust is a first-order destructive attack surface
Identity, MDM, and privileged admin workflows are not secondary concerns — they are the primary vector for achieving enterprise-scale destruction. Securing the admin plane is now a Tier-1 resilience requirement.
Insight 3
Actor messaging outpaces forensic disclosure
Handala's public claims shaped early narratives before victim-validated IOCs were available. Analysts must cleanly separate verified impact from actor propaganda when building defensive posture — overclaiming actor capabilities can distort defensive priorities.
Insight 4
Dual-use tooling complicates enforcement
NetBird and VeraCrypt are legitimate tools repurposed for destructive operations. Detection should focus on context (privilege misuse, mass staging, unusual deployment paths) rather than simple tool name blocking, which will generate excessive false positives.
Confidence Assessment
| Confidence Level | Findings |
|---|
| HIGH | A destructive incident occurred on 2026-03-11 with widespread device impact. Public technical indicators are primarily vendor-sourced and not victim-validated. |
| MEDIUM | Handala is the most plausible public attribution. Intune remote-wipe abuse is a plausible and likely contributing mechanism. |
| LOW / UNVERIFIED | Specific vendor-listed IOCs are confirmed as used against Stryker — insufficient evidence to determine. |
Sources & Citations
[C1]
Stryker disclosed a cyber incident on 2026-03-11 disrupting its internal Microsoft environment. HIGH — Stryker · Arctic Wolf Blog
[C2]
Handala publicly claimed responsibility and alleged large-scale device wiping and data exfiltration. Volumes unverified. MEDIUM — Security Affairs · HackRead
[C3]
Multiple independent reports confirm employee devices were remotely wiped or rendered unusable. HIGH — Security Affairs · BleepingComputer
[C4]
Open-source reporting and vendor analysis support Intune remote wipe as a plausible contributing mechanism. MEDIUM — Arctic Wolf Blog · BleepingComputer
[C5]
Vendor reporting associates Handala with wiper tooling, PowerShell destructive scripts, NetBird tunnelling, VeraCrypt misuse, and GPO/scheduled task deployment. MEDIUM — Check Point Research · F5 Labs
[C6]
Vendor write-ups identified Handala-associated domains, IPs, and a Telegram channel as observables. MEDIUM — Check Point Research · F5 Labs
[C7]
Actor domains handala-hack[.]to and handala[.]to were non-resolving at collection time — transient or removed infrastructure. MEDIUM — WhoisXML DNS
[C8]
Vendor-cited IPs 31[.]57[.]35[.]223 and 82[.]25[.]35[.]25 exposed Windows RPC and SMB services in internet scan data. MEDIUM — Shodan
[C9]
No victim-validated Stryker forensic IOCs were published; most indicators are vendor-sourced or actor-published. HIGH — Check Point Research · Stryker
Report generated by Protos AI Threat Intelligence | Classification: TLP:CLEAR
All IOCs are defanged. Vendor-sourced indicators should be validated against victim telemetry before operational enforcement.